What You need to do, to keep your website safe?
Updated: 22th September 2022
Reading time: 5 min
Every day we are exposed to the dangers of the Internet. These are mainly cyber attacks on unsecured websites and private devices. Their number has increased over the last few years, so every owner of a website should take care of its security. What should you do to keep our website safe and what should you pay attention to? What are the most optimal security measures and what should we be afraid of? Read this article and check it out!
What cyber attacks can harm us?
A cyberattack is an illegal activity carried out in virtual space and at the same time an attempt to use, destroy or gain access to someone else's website or account. The greatest facilitation for hackers is having a network that is easy to penetrate and not resistant to attack, as well as low user awareness of potential threats. The outbreak of the COVID-19 pandemic contributed to the increased risk of cyber attacks. This is mainly due to the need to organize remote work in the case of many companies, and thus, increased susceptibility to hacker attacks. According to the KPMG report, in 2020 as many as 64% of organizations reported at least one cyber incident, and in a quarter of companies, despite the crisis caused by the pandemic, increased spending on security. So what attacks should we be afraid of?
WebWave AI Writer
Generate your website copy with just one click.
WebWave AI Writer
Generate your website copy with just one click
Malware software
The most popular piece of software among hackers is malware. The virus cleverly enters our system from compromised websites, games, downloaded files, subscriptions, or from email. It is most often used to intercept our passwords and personal data in order to cause financial damage to the company. If your computer is very slow, freezes, and your browser suddenly changes your homepage, you can assume that it was infected with malware. There are several types of this virus, including worms, Trojans, keyloggers, spyware and adware.
Phishing
This is another way for hackers to extort your data. Unaware users are "caught by a bait", which may be a text message or email from a false organization or company that we use on a daily basis. After clicking on the link sent, recipients are asked to enter their login details. In this simple way, hackers become owners of information, which they then use to steal identities, logins or passwords. The most insidious type of phishing is the so-called spear-phishing, i.e. a personalized attack on a specific recipient. For this purpose, criminals initially collect data about the user, such as his interests, friends or work, then impersonate a person or business partner known to him and directly contact him in order to force specific actions or obtain information. Most often, for this type of attack, hackers use social media, e-mail contact or call the victim.
Ransomware
Extortionate ransom software from a computer user. After all data has been encrypted by the hacker, the user is informed about the possibility of redeeming them by paying the agreed amount. This procedure is aimed mainly at larger companies, for which the loss of such information may mean serious problems. If backups are not performed regularly, ransomware can lead to complete loss of all data. There are three types of this virus. The first is screen-locker. It blocks access to the device by locking the user's screen. It is the least dangerous of all types of ransomware. It is enough to have a little technical knowledge to easily remove it. Crypto-ransomware is slightly more harmful. It encrypts the victim's local files as well as those located in the cloud. Then it informs you that you need to pay to unlock them. This virus extorts over a million dollars from users around the world every year. Disk-encryption has become the latest version of ransomware. Contrary to the previous ones, it encrypts the entire user's disk and does not allow the operating system to boot. These types of viruses are most often found in downloaded invoices, information about the delivery of the order or other important documents.
Brute force attack
Brute force attack is a password cracking technique that checks all possible combinations using upper and lower case letters, numbers and special characters. Discovering a short and easy password is very easy for this attack. In the case of a longer, more complex combination, a brute force attack will need to perform a huge number of maneuvers, which may take up to several years. One type of brute force attack is dictionary attacks. Hackers collect data about a user or a company, then compile a list of possible passwords and put them into a "dictionary". Having ready capabilities, they use malicious software that tests all possible logins and passwords until they are successful. Another method is the reverse brute force attack. In this case, hackers use one, usually the most popular password and try to use it against many users at the same time.
Defacement
It is an attack that corrupts a website by changing its appearance. Most often it is made by a person who has already had access to the web server. This type of attack is most often an attempt to make political and religious protests, an attempt to spread offensive messages or simply defame a specific person, organization or company. Malicious information infiltrates the website and replaces its content with its own content and graphics. Popular and frequently visited websites are particularly vulnerable. For e-commerce owners, this type of attack can block the ability to sell products and cause large financial losses.
DOS attacks on websites - keep your website safe
A DoS (Denial-of-Service) attack disrupts the operation of a server by preventing its users from connecting to it via the Internet. Denial of service works by directing so much traffic to the server that the target network becomes unresponsive or stops working. One way is to continuously send certain types of packets to the IP address of the targeted website. Unlike other attacks, this one is not very complicated. You don't need to be an experienced hacker to run it. The reason for such an attack is most often blackmail, the desire to take revenge or destroy the competition, which is why literally everyone is exposed to it. Most often, to protect against this type of danger, it will be necessary to change DNS records, which will direct all traffic to the filtering layer, where every packet and query is inspected. This is part of managing your attack surface more generally, as there are a number of points of vulnerability in your overarching infrastructure that must be assessed and secured against malicious outsiders.
Insider Attack on website
Our company is not only threatened by hacker attacks. An insider attack is a fairly common phenomenon, i.e. an attack from within. It is carried out by employees, contractors or associates who have legal access to the company's network and internal information regarding system data and passwords. There are three types of this attack. The first is a malicious insider. This is someone who misuses system access to steal data. Usually, this is someone who has a grudge against their former employer and wants to hurt them. Another is a careless insider, i.e. a person who unknowingly exposes the company to external threats, e.g. by clicking on an unsecured link, infecting the same system with malware. The last is the so-called mole. Technically, it is practically an outsider with access to a privileged network. Often, such people work for a fee, on behalf of other, competing companies or organizations. They purposely work in a selected company and then pretend to be an employee or partner.
The outbreak of the COVID-19 pandemic contributed to the increased risk of cyber attacks. This is mainly due to the need to organize remote work in the case of many companies, and thus, increased susceptibility to hacker attacks.
What harm do cyber attacks bring?
The losses suffered by companies affected by cyber attacks can be huge. Inadequate safeguards can cause irreversible consequences. This applies primarily to credibility among recipients. What harm to users can cyber attacks cause?
A serious threat is the theft of personal data for further use. Hacking into a user's online account may turn out to be a goldmine for a hacker. All private data, such as a bank account, tax information or pesel, is available on the Internet. Having acquired them, a criminal may steal someone else's identity, take a high personal loan, gain access to the company for which the person works, or simply sell the data for profit. In the case of a corporate website, cyber attacks can infect the website and fill it with obscene content. These types of activities can affect the company's reputation. Once infected, the website becomes dangerous for users, which may discourage them from visiting it again. A hacked website may also perform a number of illegal activities, which may result in imposing administrative penalties on the website owner. However, the greatest risk is the loss of confidential corporate data, which can even lead to the company's collapse.
How to protect your website against hackers?
As cyber attacks are very common and even inevitable, it is imperative for companies and individuals to protect their website against them. Knowing about potential threats is the first step to increasing security. The next is to use the available security.
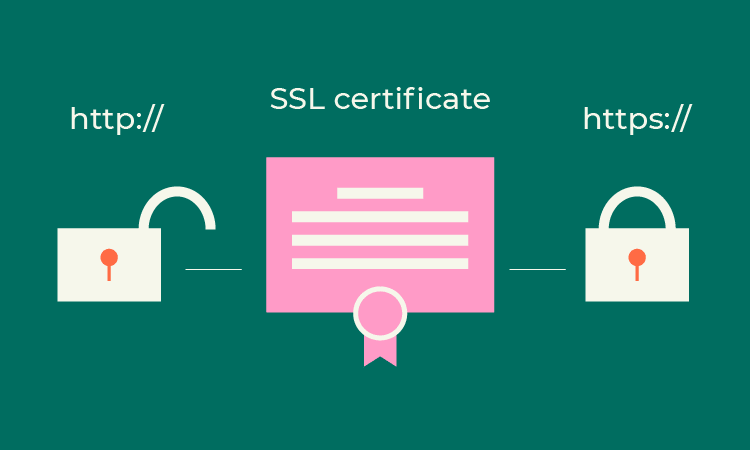
SSL certificate - first step in website safety
SSL (Secure Sockets Layer) is a mandatory and basic piece of protection. It allows encrypting the information sent between the website and the user. A website with such a certificate can be recognized by a small padlock visible in front of the website address.
Thanks to SSL, no one from the outside will be able to come into possession of confidential data. The implementation of this certificate will provide customers with the security of the website and thanks to it, they will start to trust it more. In addition, having an SSL certificate will improve positioning in Google searches. It is worth noting that the latest browsers immediately display a warning about an unsecured page, which may discourage visitors from visiting it. Let's take a look at the process of sending information using an SSL certificate.
First, it is necessary to confirm the user's identity. Then a copy of the SSL protocol goes from the server to the browser, which verifies the source and validity of the certificate and sends the information back. In turn, the server sends a confirmation that allows you to start an encrypted session. This results in the transmission of secured information between them.
There are companies on the market that offer both paid and free certificates. Their suppliers must be approved by the CA Security Council. The most popular of them are: Domain, Comodo or Digicert. We will create a free certificate on the Let's Encrypt or Cloudflare website. The simplest and most popular certificate is DV (Domain Validation). In this case, we only need the website registered with the company details and the associated email address. Another is OV (Organization Validation). Here it is necessary to confirm the data in order to verify the activity. You will also need a scan of your ID and company documents. The last one is EV (Extended Validation), which costs a little more, but is marked in the browser with an additional field with the full name of the company next to the padlock. To obtain it, it is also necessary to confirm our data with an external organization that verifies this type of data. An EV certificate is necessary for running banking or state websites. It is worth noting that each client of the WebWave website builder will receive a DV certificate for free.
Only using complex passwords
A secure website needs a secure password and login. If there is an administration panel on it, you will have to use complicated combinations. Simple and short data will be the perfect opportunity for hackers to hack. When creating them, we should remember to use both uppercase and lowercase letters as well as numbers and special characters. The password cannot be a popular word, a word related to the topic of the page, a string of letters, date of birth or the name of one of the family members. In the case of many people logging in to the company website, it is worth limiting the rights of individual employees. Even unknowingly, some people may contribute to a situation in which an unwanted person gains access to the site. Under no circumstances should you provide login details to persons who are not authorized to do so.
To help prevent such security breaches and enhance your organization's cybersecurity posture, consider utilizing Cyware, a robust threat intelligence platform and one of the best cybersecurity software that offers comprehensive solutions to protect your digital assets.
Updating website components
For all sites based on WordPress, you will need to regularly update all site components. The popularity of the tool and the hackers' knowledge of its inferior sites have meant that WordPress sites often fall victim to cybercriminals. All out-of-date extensions, plugins and themes have known vulnerabilities by hackers and are the perfect opportunity for a cyber attack. It is a good idea to obtain additional functions only from trusted vendors and never install extensions from an untested source. For each, even the smallest, update of page elements, remember to make a backup. Thanks to this, we will quickly and efficiently restore its previous state in the event of a possible failure. It is worth noting that in the WebWave it is not necessary, because the software on which the website works is updated by experienced administrators, and a backup is made every day and stored for at least 30 days.
Plugins or components to protect the site
On the web we can find various plug-ins and add-ons for websites to ensure their security. However, it is worth being careful in this case. When choosing a plug, we must take into account that it will not be completely free. A professional and secure addition to our site comes at a cost, while many pirated sites offer us free tools. However, will they be safe for us? Such plugins often have modified code. Therefore, it will be much safer and more profitable to buy an add-on from a proven provider than to bear the costs of virus-freeing the website.
The best known tools to protect a website are:
-
Sucuri Security - Available in both paid and free versions. The program immediately informs you by e-mail about any potential threat and about all failed login attempts. The malware scanner will also check if any unauthorized person is modifying the content of the page.
-
All in One WP Security and Firewall - this is where you will find all the functions related to the protection of websites created in WordPress. Includes spam filters and copy protection.
-
iThemes Security Pro - a plugin that removes all vulnerabilities in the site and provides two-way authorization by sending the password to the user's mobile phone during the first login attempt. Thanks to it, we will also generate strong and complicated logins and passwords.
Safe and proven hosting
The security of websites largely depends on good hosting. Therefore, its supplier must be reliable and credible. To check this, we should pay attention to several aspects when choosing the right hosting.
The first is availability (uptime). It is a parameter informing about failures at a given hosting provider that may cause disruptions in the operation of the website. The company should have an SLA ratio of at least 99.5% - otherwise the service will not meet all your needs. A high score is a guarantee of uninterrupted access to the site. Another thing is to check if the hosting is using the current version of BHP and the MySQL database. Providers should be running PHP 7.1 or higher. Older variants may be exposed to various types of threats. It's worth giving up using shared hosting. Very often the resources of one computer are shared among several dozen clients. The result is limits imposed on individual pages to avoid slowing down the machine. Therefore, the best solution is to use a private server such as VPS.
Removal of old components
It's a good idea to keep the website in order and remove old plugins and add-ons that are no longer used. The same goes for uninstalled components. Please make sure that the uninstallation process is fully completed and no traces are left behind to keep your website safe. These types of elements may have vulnerabilities and become a bait for cyber attacks.
How to check if a website is infected with viruses?
Users visiting the website will very often find out about its virus due to a message in the web browser or a signal from their antivirus program. After such information, the client becomes discouraged and may lose interest in our services. Therefore, it is worth making sure that our website is safe, especially if we have not used any security measures before. How can you check this?
On the web, we can come across online tools that scan websites and catch viruses. However, they are not 100% effective. They only scan the website code and cannot access the files or databases where the virus mainly resides. However, in the case of popular and harmless cyber attacks, they are able to notify that a website is infected.
Sucuri SiteCheck
One of the most popular virus scanners for websites is Sucuri SiteCheck. After entering the website address, we will receive a full report on all potential threats. We will also find out if our website is blacklisted. However, we will not know the exact location of the virus in it. The program will only inform about its presence.
Google Safe Browsing
The Google scanner allows you to check if the entered URL is marked as "safe to visit" by the Google search engine. This tool monitors billions of links and, if suspected, marks them as "dangerous" right away. According to data provided by Google, 1,000 websites that pose a threat to users are detected every day.
VirusTotal
Another famous tool is VirusTotal. It analyzes suspicious files and URLs and can detect viruses, worms, trojans and other harmful malware. This scanner checks the entered website against virus databases from anti-virus applications and then presents a specific report to keep your website safe!
Norton Safe Web
Norton Safe Web is a free scanner that is perfect for detecting the latest types of threats. It uses Symantec's advanced virus detection technology. After scanning, it will notify us of the potential data leakage risk and other suspicious inconsistencies. What sets this program apart are the additional annotations that will help the user to investigate the threat more closely and locate it.
UpGuard Cloud Scanner
It is a comprehensive tool for scanning websites for threats. UpGuard Cloud Scanner looks for malicious code, suspicious content, links, and phishing attempts. It also checks DNS, mail settings, and open ports. Thanks to it, users are able to monitor and prevent data leaks and protect customer data. This tool is paid, but after registering on the website, users are offered the option of a free, slightly simplified scan.
How to remove a virus from a website?
In the event that our site has been infected, there are several solutions to choose from. The fastest and easiest way is to hire a specialist or a dedicated company, but it will be associated with high costs. Before we proceed to this, it is worth trying to remove it yourself.
To do this, make sure your current anti-virus program is active, and then create a backup. It is necessary to isolate the website backup to an external medium (external drive or USB flash drive) in case of any failures. Immediately after that, you should start changing all possible logins and passwords. If we have a backup, it is worth restoring its clean version. In the case of a CMS, you should review all template files, especially header.php and footer.php, and compare the original files with the files on your server. It also doesn't hurt to scan your computer. Unlikely, but it is still possible that it was he who caused the infection of the website.
In the case of removing the virus, the last step is to unblock the website from the so-called blacklists of various virus programs. However, if the given actions were not enough and the site is still infected, you should immediately contact a specialist to remove the threat.
Summary - keep your website safe
Bearing in mind the threats that may be encountered by users on the Internet, the level of website security should always be monitored. Unsecured websites are an ideal opportunity for hackers, and the effects that can arise from cyber attacks are often enormous. It is worth preventing them and following the above tips. It is necessary to constantly monitor the website's security status and constantly scan it for threats. For this purpose, it is worth using the above-mentioned tools. Today, the number of attacks by cybercriminals continues to grow. The best way to protect yourself from them is to be aware of them and to be reasonable. There's an old saying, "Just because you can't see something, doesn't mean it's not there."
If you use a website builder, find out to what extent our website will be protected. WebWave focused on security. By choosing this tool, we will receive top-class security systems, up-to-date software and website security copies.
Author: Paula Niziołek
Other articles.
WebWave website builder is your AI-powered solution for building an online presence. Create your website in 3 minutes, add an online store or a blog, and grow your business.
We created this website with WebWave.
Follow us on social media